Voatz
Voatz Mobile App
Make / Model: Voatz Mobile App
Equipment Type: Internet Voting System
Back to Voting Equipment Database
Overview

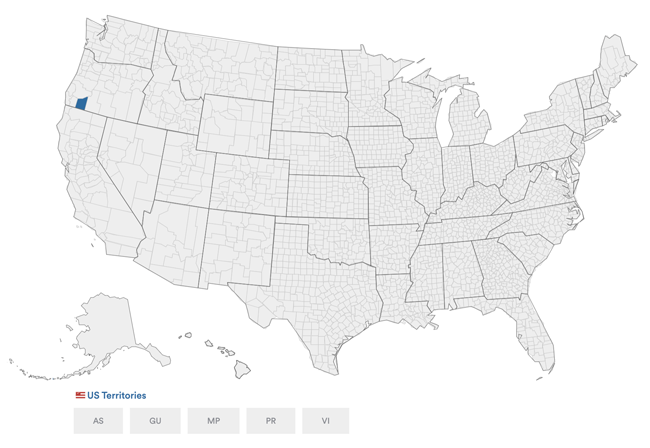
Voatz is a mobile phone application for ballot marking and the electronic return of voted ballots (internet voting). Voatz has been piloted in a handful of counties and in the state of New Jersey. In 2020, Voatz is only available to Uniformed and Overseas Citizens Absentee Voting Act (UOCAVA) voters and voters with disabilities in Utah County, Utah.
To use the Voatz mobile app, the voter’s phone must support biometric authentication (fingerprint and facial recognition) and be running the latest version of its operating system (e.g. iPhone 5 or newer or select Android smartphones running Android version 8.0 or newer). The app supports Voice Control on iOS and TalkBack on Android, configurable font size, and Speech-to-Text for write-in candidates. In 2020, Voatz is available in English and Spanish.
Voting Process
To use Voatz, a voter must download the mobile app on their device, create an account with their mobile number and email, and choose a security PIN. The voter usually receives the invitation to download the app from their county at the beginning of the early voting window, if the state allows early voting. If the voter already has the app downloaded, the voter will receive a red badge notification from their Voatz app to indicate that they now have the option to cast a ballot.
For authentication purposes, the voter must complete a three-step process, which is then “paired” to the voter’s device biometrics or PIN: the voter scans their state driver license or passport, takes a live video “selfie,” and touches their fingerprint on the fingerprint reader on their phone. After the voter’s identity is verified and linked to the voter’s fingerprint, Apple FaceID image, or PIN, the voter’s identifying document images are expunged from the app. Thenceforth, Voatz to use the voter’s smartphone thumbprint, Apple FaceID image, or PIN capabilities to authenticate the voter.
To vote using the Voatz app, the voter views candidates or ballot initiatives one contest at a time. When using a screen reader, the voter will hear how many contests there are total and which one they are currently viewing (e.g. “contest one of five). When viewing a contest, how many candidates are in the contest, and whether the candidate’s name being read to them has been selected. To select a candidate, the voter taps or double-taps the candidate’s name and the oval to the left of their name is filled in.
To write in a candidate, the voter can use their phone’s keyboard or use their phone’s dictation tool. Voters are prevented from overvoting and receive a message that the maximum number of selections have been made. The voter is also warned of undervotes with an “incomplete ballot” message.
The review screen allows the voter to review a summary ballot with only their selections. A voter using a screen reader will hear their selections and whether they have left any contests unvoted. From the review screen, the voter can make changes to their selections. When the voter is satisfied with their ballot, they select “Submit Ballot.” The voter is prompted to enter their eight-digit Voatz PIN.
After submitting their ballot, the voter receives via email an “official ballot receipt,” which is a PDF summary ballot of their choices. Adobe Reader can read the ballot back to the voter. The voter’s summary ballot is also sent to the elections office via blockchain servers. After every blockchain server has reviewed and confirmed the voter’s ballot, the voter receives a confirmation message on the Voatz app. The voter will not be allowed to vote again. The elections office then prints out the version of the voter’s ballot received on its end.
Videos
Voatz App Helps People Cast Ballots on Smartphones
References
Resources
Specter, et al., The Ballot is Busted Before the Blockchain: A Security Analysis of Voatz, the First Internet Voting Application Used in U.S. Federal Elections (2020)
Voatz Mobile Voting Platform, An Overview: Security, Identity, Auditability (2020)
Trail of Bits, Voatz Security Assessment Volume I of II: Technical Findings (2020)
Trail of Bits, Voatz Security Assessment Volume II of II: Threat Modeling Findings (2020)
National Cybersecurity Center, The Denver Mobile Voting Pilot: A Report (2019)
National Cybersecurity Center, Audit Summary of the Utah County Primary Election (2019)
Voatz, UNDER THE HOOD: The West Virginia Mobile Voting Pilot (2019)
Security Concerns
Attacks on a Voter’s Phone Could Change and Expose a Voter’s Selections
Michael A. Specter, James Koppel, and Daniel Weitzner completed a security analysis of the Voatz mobile app based on a reverse engineering of the Android application, the available documentation of the system, and a clean-room reimplementation of Voatz’s server. The authors of the analysis found that an attacker with root privileges on a voter’s device could disable all of Voatz’s host-based protections to stealthily control the voter’s selections and what the voter sees on their own device, expose the voter’s ballot, and exfiltrate the voter’s PIN and other data used to authenticate the voter to the server.
Because Voatz does not limit the number of times the voter’s PIN can be attempted and because the PIN is limited to eight numeric characters, Specter, Koppel, and Weitzner found that a brute force attack could easily rediscover a voter’s PIN by repeatedly generating keys and attempting to decrypt the database. Although an attacker would likely need access to the database, they would not necessarily need access to a voter’s device to make this attack as the encrypted database file can be exported. The security analysis authors implemented a prototype of this type of brute force attack from a commercial off-the-shelf (COTS) laptop and were successful in approximately two days.
Limitations of Blockchain
According to the authors of the Trail of Bits security analysis, storing data on a blockchain maintains an auditable record, but comes at the expense of privacy and increased possibility of attacks. Because voters do not connect directly to the blockchain, they cannot independently verify that their votes were properly recorded.
An “Anonymous ID” is randomly generated by the backend and sent to a voter on their ballot receipt. However, the voter’s customer ID and device ID are linked to the voter’s personally identifiable information. The Trail of Bits security analysis authors found that a Voatz administrator with access to the backend server could observe API requests when ballots are submitted in real time and deanonymize votes. The Voatz system also does not appear to prevent voters from being identified by time at which their ballot was recorded on the blockchain, meaning a voter’s idendity could be discovered by the approximate time of their vote.
Specter, Koppel, and Weitzner found it unlikely that every interaction a voter has with the app is stored via the blockchain. Voatz’s documentation of the West Virginia pilot indicates that the verifying servers are split equally between Amazon AWS and Microsoft’s Azure, meaning that the system is vulnerable to Microsoft or Amazon surreptitiously adding resources and executing a 51% attack.
Attacks on the Server Could Expose a Voter’s Selections and Prevent a Voter from Submitting their Ballot
In their security analysis, Specter, Koppel, and Weitzner discovered that an adversary with the ability to view a voter’s network activity, without access to any key material, could still infer the voter’s selections. When a voter submits their ballot to the server, the voter’s choices are listed in summary ballot form, with only the candidates selection visible to the voter. The voter’s selections, however, include the entirety of the metadata provided by the server about each candidate, so the length of the ciphertext clearly leaks which candidate the voter selected and the voter’s choice is easily distinguishable. If the voter does not select a candidate in a contest, the app sends the server an empty list.
To learn a voter’s selections in this way, an attacker would need to be a registered voter, have previously witnessed a registered voter’s ballot options, or have witnessed a voter casting a ballot in a particular way and recording the result. The attacker would be able to detect a voter’s intent before the ballot arrives at the server, so if the attacker is capable of blocking the ballot’s path to the server, they could prevent the voter from submitting their ballot. If done repeatedly, this could be enough to prevent the voter from casting their ballot entirely.
A Voter’s Personal Information and Location Could be Exposed
Specter, Koppel, and Weitzner found that a voter’s email, physical address, birth date, IP address, current photo, geolocation, a photo of the voter’s ID, their device’s model and OS version, and preferred language are all sent to Voatz and Jumio, the provider of the ID scanning and validation solution. If an attacker worked within Jumio, Jumio could refuse to validate certain voters. When a voter first logs in to the Voatz app, the app requests permissions to read the user’s GPS. Specter, Koppel, and Weitzner note that UOCAVA voters’ precise locations could be leaked to adversaries, exposing information about U.S. military movements.
Manufacturer Profile
Voatz was founded in 2015 after its founders won the ‘Hack to the Future’ hackathon at SXSW in 2014 with an idea for mobile voting and preventing voter coercion. Voatz has been the recipient of the Microsoft Civic Innovation Award in 2017 and the Innovative Entrepreneurship in Blockchain Award (Public Sector Services) in 2019, and was a finalist at the GSMA Mobile World Congress 2020 Awards for Best Mobile Innovation for Accessibility and Inclusion.